The internet has become increasingly critical for survival during the COVID-19 pandemic and is a necessity with millions of people working remotely. A recent discovery by Digital Revolution, a Russian hacker group, reveals that Russia’s national intelligence service (FSB or Russia’s Federated Security Service) has been working on an Internet of Things (IoT) botnet project that could shut down the internet.
Botnet and IoT relevancy
The IoT is a term coined to describe everyday things such as light bulbs, medical devices, and wearable devices that are capable of sending and receiving data via the internet. It is estimated by Gartner, a technology research company, that this year there are at least 20.4 billion IoT devices in use. Unfortunately, these devices often have little to no built-in security and thus, are increasingly being leveraged for botnets. A botnet refers to a group of network connected devices that have been infected with malware and are under control by a threat actor. A botnet can be thought of as the virtual equivalent of a marionette, but the controller has mal intent.
In 2016, a strain of malware called Mirai was used to launch a large-scale distributed denial of service (DDoS) attack. It crippled major websites like Krebs on Security and took down several high-profile facilities such as cloud and Domain Naming Services (DNS). However, what is remarkable about the attack is that it was entirely carried out by seemingly harmless IoT devices. Mirai scans the internet for IoT devices operating the ARC processor (a stripped-down version of Linux OS) and if the default username and password combination is not changed, it logs into the device and infects it. Upon infection, the device becomes a “bot” and sends a signal to a preconfigured Command and Control Server (C&C). This server acts as a director of the bot and can command it to send spam, mine cryptocurrency, or even unite with other bots for a DDoS attack. At its peak, Mirai infected roughly 600,000 IoT devices.
Securing IoT is typically overlooked by vendors because there is little incentive to invest in the security of low-cost devices and there is not an enforced global IoT security standard. Additionally, even if patches are released, users often do not have the skills to update nor the encouragement to apply patches because infected devices while they might perform more sluggish, will typically operate as intended.
Fronton – Russia’s IoT Botnet Weapon
While nothing has been confirmed, 12 documents released by Digital Revolution, strongly suggest that the FSB has decided to create its own Mirai tool. The documents refer to variations of a project called Fronton, Fronton- 3D, and Fronton-18.
Within one document a procurement order was unveiled from an internal FSB department unit 64829 that references Mirai – further proving that the FSB is trying to develop something similar. In another document, there are details that Fronton botnet can carry out dictionary attacks against IoT devices which would allow for a higher infection rate. This is treacherous because once an attack is successful the device could be enchained into a botnet that could conduct damage far surpassing that of Mirai.
Within the uncovered documents, it is evident Fronton targets Linux based smart devices and unfortunately, Linux devices account for the majority of IoT systems in use today. Additionally, Fronton is particularly more menacing when compared to Mirai because it eliminates the single point of failure commonly associated with botnets. That is, the location of the C&C server used to convey the attacker’s commands is obfuscated. This is an astute take on IoT malware as a botnet is only effective as long as there is a controller. In the case of Fronton, the documents list that Fronton can operate surreptitiously for an indefinite period because its C&C server’s real location is hidden behind a network of VPN and proxy servers.
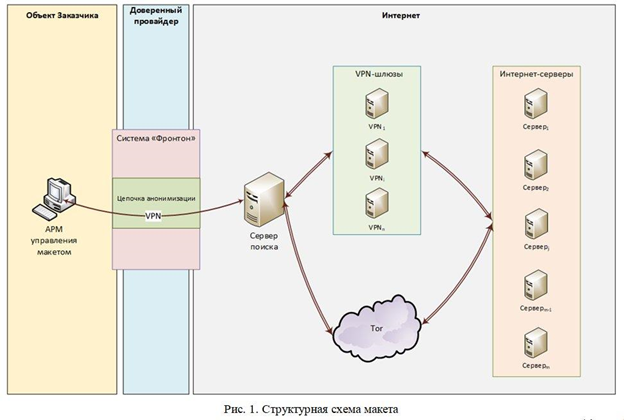
Image via Digital Revolution
How does the IoT relate to a Russian botnet and takedown of the internet?
Whether or not an individual uses IoT devices, Fronton has the potential to impact every person’s life. Should its creators choose to, Fronton could be pointed to attack internet service providers, send spam email, bring down websites, perform click fraud, and execute other nefarious tasks. The exposed Digital Revolution documents explicitly state, “an attack on national DNS servers can make the Internet inaccessible for several hours in a small country.” Thereby acknowledging the power, they have with Fronton.
Justin Sherman, a global internet governance researcher, insists that exploiting hacked IoT to bring down a small country or group of services follows Russia’s previous cyber behavior.
In August 2019, Microsoft spotted attacks on popular IoT devices that were used as entry points for victims’ internal networks. Russian state-backed IoT hackers are nothing new, but particularly frightening now because the world relies on the internet. Moreover, with millions of Americans working from home, the United States has never been this dependent on the internet.
DNS providers and similar technological hubs are what make the internet usable for people. If Fronton was pointed towards the US, the most damage it could create is a short-term inconvenience. However, other countries do not have a robust infrastructure and could be completely taken down. Moreover, debilitating core technological infrastructure creates a path for Russia to accomplish its nation’s objectives in which case nothing is stopping Russia from using its DDoS-capable tool to assert power and target essential internet infrastructure across multiple countries.
Why take down the internet?
The easiest way to take a network off the internet is by launching a DDoS attack. While their objectives are unclear, using the contended Fronton botnet presents Russia with the capacity to commit espionage against rival countries, steal intellectual property, or gather intelligence. In which case the documents leaked by Digital Revolution only demonstrate that threat actors like Russia have the capability to weaponize innocuous IoT for malicious events and like frankly launching DDoS attacks on critical internet services is easier than most people imagine.
Is your organization being proactive with methods to detect and prevent DDoS attacks? Contact Silent Sector for support with strengthening your cybersecurity program.


